mTLS (Mutual TLS) is an enhanced security protocol that requires both client and server to authenticate each other's identity. This article explains what mTLS is, how it works, its pros and cons, and a deployment guide.
High-Speed Proxy - Ready to Try?
ALGO Proxy offers residential, datacenter & 4G proxies in 195+ countries
What is mTLS?

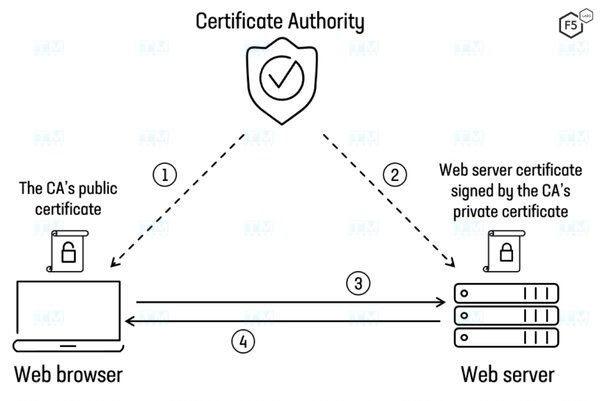
mTLS (Mutual Transport Layer Security) is an enhanced version of TLS that requires both client and server to authenticate each other's identity through digital certificates. While standard TLS only requires the server to prove its identity, mTLS adds the step where the client must also present a valid certificate.
Digital certificates are issued by a trusted Certificate Authority (CA) and contain identity information, domain name, and validity period. mTLS creates a dual security layer — ensuring both parties are legitimate before exchanging data.
How mTLS Works
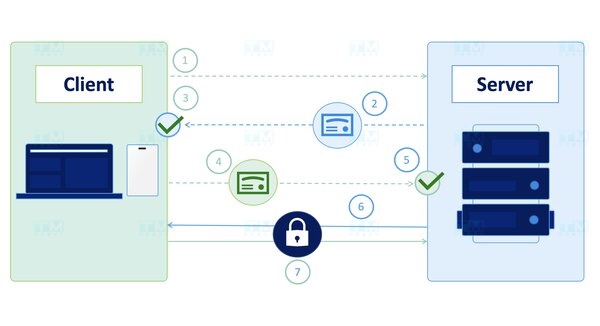
The mTLS handshake process consists of these steps:
- Client sends connection request (ClientHello) to server with a list of supported cipher suites.
- Server responds (ServerHello) with the selected cipher suite and sends its SSL certificate.
- Client verifies server certificate — checks CA, validity period, domain name.
- Server requests client certificate (CertificateRequest) — this is the step that differentiates mTLS from TLS.
- Client sends its certificate to the server.
- Server verifies client certificate — checks CA, validity period, access rights.
- Encrypted channel is established — both sides exchange session keys to encrypt data.
The entire process takes just a few hundred milliseconds. After successful handshake, all transmitted data is encrypted and authenticated.
Benefits and Applications
Two-way Authentication: Both client and server must prove their identity, preventing unauthorized access and impersonation.
Man-in-the-Middle (MITM) Protection: Attackers cannot intercept connections because they lack valid certificates to pass authentication.
Data Protection in Transit: End-to-end encryption — even if data is intercepted on an insecure network, it cannot be decrypted.
Common Applications:
- Microservices: Authentication between services in Kubernetes, Istio service mesh.
- Zero Trust Network: Every connection must be authenticated, no default trust.
- Internal APIs: Securing APIs between backend systems not exposed to public Internet.
- IoT: Authenticating IoT devices connecting to central servers.
- Finance and Healthcare: Compliance with PCI DSS, HIPAA security regulations.
mTLS Deployment Guide

Step 1 — Install server certificate: Choose a trusted CA (Let's Encrypt, DigiCert, or Internal CA), create a CSR (Certificate Signing Request), and install the SSL certificate on your server.
Step 2 — Configure server to require client certificates: Update your web server or application configuration to enable ssl_verify_client on (Nginx) or SSLVerifyClient require (Apache). Specify the CA trust store containing the list of accepted CAs.
Step 3 — Install certificates on clients: Issue certificates to each client from an internal CA or trusted CA. Configure client applications to use their certificates when connecting to the server.
TLS vs mTLS Comparison

| Criteria | TLS | mTLS |
|---|---|---|
| Authentication | One-way (server only) | Two-way (server + client) |
| Client Certificate | Not required | Required |
| Security | Encrypts data in transit | Encryption + two-way authentication |
| MITM Protection | Partial | Stronger |
| Complexity | Easy to deploy | More complex |
| Performance | Low overhead | Higher overhead (handshake) |
| Certificate Management | Server only | Server + all clients |
| Use Cases | Websites, email, apps | Microservices, APIs, IoT, Zero Trust |
When to use TLS: Public websites, standard web applications, email — where only server authentication is needed.
When to use mTLS: Microservices, internal APIs, IoT, financial systems — where both parties need authentication and high security.
Conclusion: mTLS is a powerful security solution with two-way authentication, especially suitable for microservices, internal APIs, and Zero Trust architecture. While more complex to deploy than TLS, mTLS provides superior security for high-requirement systems.