A Botnet is a network of malware-infected devices that are remotely controlled to carry out DDoS attacks, steal data, and perform various other illegal activities. This article provides a detailed analysis of botnet structure, classification, impact on businesses, and effective countermeasures.
High-Speed Proxy - Ready to Try?
ALGO Proxy offers residential, datacenter & 4G proxies in 195+ countries
What is a Botnet?
What is a Botnet? A botnet, also known as a robot network, is a collection of internet-connected devices -- including computers, smartphones, servers, and IoT devices -- that have been infected with malware. All of these devices are remotely controlled by one or more attackers. These devices are called "bots" or "zombies," and the attacker behind them is known as the "bot herder."
Once a device becomes a bot, it can participate in numerous illegal activities on the internet. For instance, an attacker can command millions of bots to send spam, launch Distributed Denial of Service (DDoS) attacks, steal personal information, and carry out many other malicious activities. To put it simply, imagine a zombie army from a horror movie, where each zombie represents a malware-infected device, and the controller is an evil sorcerer ready to command them to commit crimes.
The History of Botnets
Botnets first appeared in the 1990s but have only truly exploded in recent years alongside the development of technology and the internet. Initially, bots were typically created to perform simple tasks such as automating web activities. However, once bad actors recognized the potential of bots for carrying out cyberattacks, they began developing more sophisticated malware to turn devices into tools for criminal activity.
What is the 500 Internal Server Error? How to Fix It Effectively
The Evolution of Botnets
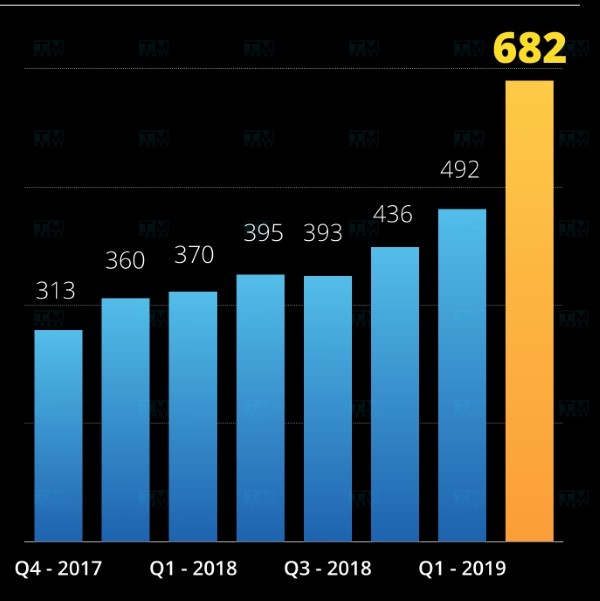
Today, botnets have become an integral part of cybercriminal operations. With the rise of IoT-connected devices, the scale of botnets has grown significantly, and their attack capabilities have become increasingly sophisticated. Many international criminal organizations now use botnets as their primary tool for executing fraud schemes and financial attacks.
DDoS Botnet Attacks
DDoS (Distributed Denial of Service) is one of the most common forms of cyberattack today, particularly through botnets. A DDoS attack occurs when a system is bombarded with massive amounts of fake traffic from millions of bots simultaneously, saturating bandwidth and disrupting services.
How DDoS Botnet Attacks Work
A DDoS attack begins with the attacker controlling a network of bots through malware. After infection, the bots wait for commands from the bot herder. When the command is issued, all bots simultaneously flood a single server with requests, overwhelming the system and making it unable to respond to legitimate requests from real users.
Consequences of DDoS Botnet Attacks
The consequences of DDoS attacks can be extremely severe, especially for businesses and organizations. These attacks not only cause service disruptions but also damage the reputation and brand image of the business. Revenue can decline, and customers may lose trust in the company's security capabilities and reliability.
Objectives of Botnet Attacks
Every botnet attack has a clear objective, depending on the attacker's intent. Some common objectives include:

Information Theft
Many botnet attacks aim to steal personal and financial information from users. Attackers can use bots to collect login credentials, credit card numbers, or other sensitive data.
Generating Revenue from Illegal Advertising
Some attackers use botnets to generate fake clicks on online advertisements, earning money from pay-per-click programs. This not only harms advertisers but also degrades the quality of service for real users.
Sabotage and Disruption
Beyond financial gain, some botnet attacks aim to sabotage or disrupt a particular organization or individual. This can cause damage to reputation, brand image, and even threaten the survival of a business.
Classification of Common Botnets Today
Botnets can be classified based on their purpose and method of operation. Below are the most common types:
DDoS Botnets
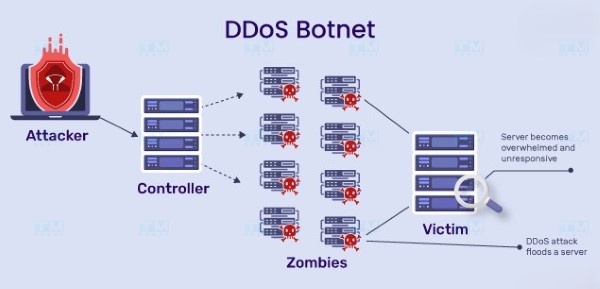
This type of botnet is primarily designed to carry out DDoS attacks. They can send a massive volume of requests to a server, causing overload and forcing the server to shut down.
What is a Rotating Proxy? Benefits of Using Rotating Proxies
Spam Botnets
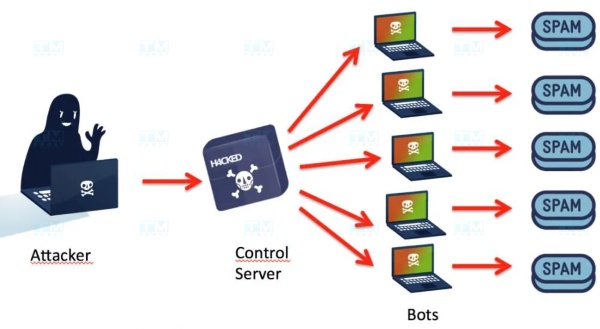
These botnets are used to send spam to millions of users. The spam messages typically contain malicious links or attempt to deceive recipients.
Click Fraud Botnets
This type of botnet is highly sophisticated, programmed to generate fake clicks on online advertisements, creating illegal revenue for the attacker.
Stealer Botnets

Stealer botnets specialize in stealing personal information, passwords, and credit card numbers from users. They are typically installed on victims' devices without their consent.
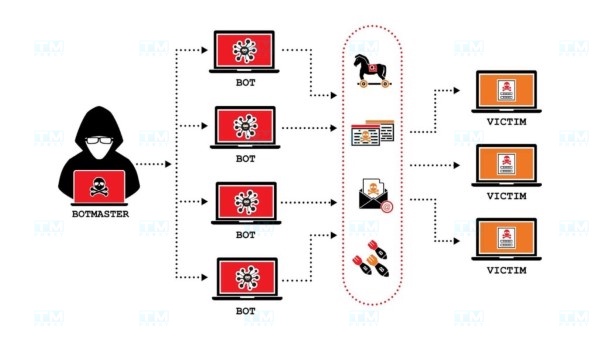
Botnet Structure
The structure of a botnet resembles a network, with bots located at many different positions and capable of interacting with each other. There are two main models of botnet structure:
Client-Server Model
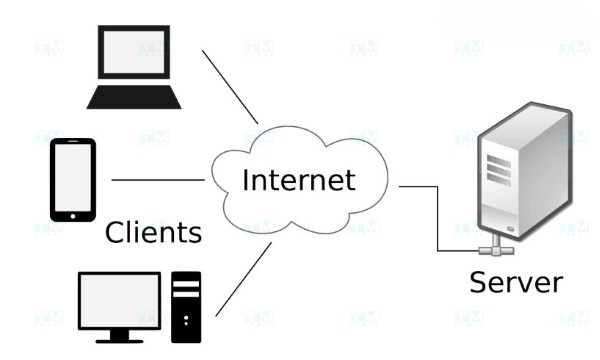
In this model, the bot herder controls a central server, and the bots connect to this server to receive commands. This model is typically easier to manage but has a major weakness: if the central server is discovered and taken down, the entire botnet can be destroyed.
Peer-to-Peer Model
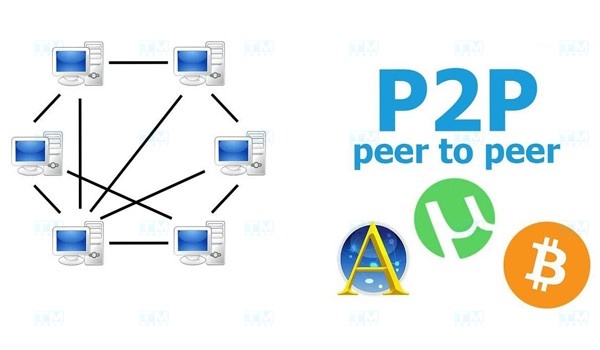
The peer-to-peer model allows bots to communicate directly with each other without needing a central server. This enhances the resilience of the botnet, because even if one bot is removed, the other bots can continue operating and relaying commands to each other.
Impact of DDoS Botnets on Businesses
The impact of DDoS botnet attacks on businesses should not be underestimated. They can cause numerous serious problems:

Service Disruption
One of the first consequences businesses face is service disruption. This occurs when servers cannot process customer requests, preventing customers from accessing the services or products they need.
Loss of System Control
DDoS attacks can cause businesses to lose control of their systems. When a botnet launches an attack, administrators struggle to identify the cause and restore the system quickly.
Financial Losses
Financial losses from DDoS attacks can be substantial. Beyond lost service revenue, businesses must also pay significant costs to remediate the damage and secure their systems.
Data and Information Security Vulnerabilities
DDoS attacks are not limited to disrupting services. In some cases, attackers can exploit the chaos to infiltrate systems and steal critical information.
Common Types of Botnet Attacks Today
There are many types of botnet attacks that businesses need to be vigilant about. Below are the most common types:
DDoS Attacks

As mentioned earlier, DDoS is one of the most common forms of attack. It involves the coordination of millions of bots to paralyze a service or website.
Spam Distribution Attacks
Attackers can use a botnet network to send millions of spam emails, annoying users and potentially containing malware designed to steal information.
Keylogging

Keylogging is a method of collecting personal information by recording every keystroke a user makes. Attackers can use bots to run keylogger software and harvest sensitive data.
Identity Theft
Botnets can also be used to carry out identity theft attacks, where attackers steal personal information to forge identities and conduct illegal financial transactions.
Pay-Per-Click Exploitation
As mentioned, attackers can generate fake clicks on online advertisements, earning money illegally.
Botnet Propagation

Some bots can be programmed to spread malware to other devices, creating new bot networks and making control and prevention increasingly difficult.
Adware
Adware can be distributed through botnets, causing annoyance to users and degrading device performance.
DDoS Botnet Prevention Measures
To protect businesses from DDoS botnet attacks, effective prevention measures are essential:
Use Firewalls and Intrusion Detection Systems (IDS/IPS)
Firewalls help control traffic entering and leaving the network, while IDS/IPS can detect and respond quickly to attacks.
Use Web Application and API Protection (WAAP) Solutions
WAAP provides additional layers of protection for web applications and APIs, helping to block security attacks before they can cause damage.
Use Content Delivery Networks (CDN)
CDN networks help distribute traffic across multiple servers, reducing the load on the main server and preventing paralysis from DDoS attacks.
Monitor Network Traffic
Regular network traffic monitoring helps businesses detect abnormal activities and respond with timely countermeasures.
{{< test-result title="So sanh cac loai Botnet" headers="Tieu chi|Botnet DDoS|Botnet Spam|Botnet Click Fraud|Botnet Stealer" row1="Muc dich|Lam te liet dich vu|Gui thu rac|Nhan chuot gia mao|Danh cap thong tin" row2="Muc do nguy hiem|Rat cao|Trung binh|Trung binh|Cao" row3="Doi tuong|May chu, website|Email nguoi dung|Quang cao truc tuyen|Tai khoan ca nhan" row4="Kha nang phat hien|Trung binh|De phat hien|Kho phat hien|Kho phat hien" row5="Bien phap phong chong|Firewall, CDN, IDS|Bo loc spam|Phan tich hanh vi|Antivirus, 2FA" />}}
Conclusion: Botnets are networks of malware-infected devices that are remotely controlled to carry out cyberattacks. Understanding the structure, classification, and impact of botnets helps businesses proactively defend and protect their systems against cybersecurity threats.